Reimaging a computer is a term that resonates significantly in the realm of computing and IT solutions. The action of reimaging entails restoring a computer system to a previous state by replicating a standard image of the operating system, applications, settings, and—occasionally—data. This process is common in both individual and organizational settings and is often undertaken for a variety of reasons, such as troubleshooting software issues, enhancing system performance, maintaining security, or preparing devices for redistribution.
To comprehend the implications of reimaging a computer, one must first grasp what a ‘system image’ entails. A system image is a complete copy of all the data on a computer’s hard drive, including the operating system, configuration, software programs, and personal files. When a computer is reimaged, this image is used to overwrite the existing data, reforming the system into its original specifications. Thus, any glitches or corruption that existed in the previous setup are eliminated.
When Should You Consider Reimaging?
The decision to reimage a computer should be deliberate. There are several scenarios where reimaging is particularly beneficial:
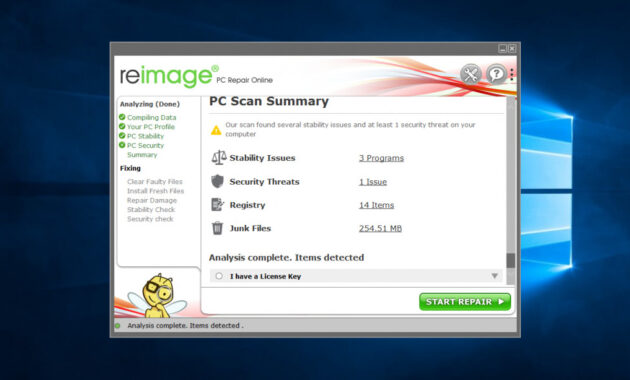
- System Malfunctions: Frequent crashes, sluggish performance, or persistent errors can be indicative of deeper system issues. Reimaging can often serve as an effective remedy.
- Malware Infections: If a system is compromised by viruses or other malicious software, reimaging provides a clean slate, eliminating any unwanted programs or files.
- Outdated Configurations: As software updates and new applications arise, an OS may become cluttered or outdated. Reimaging allows users to start afresh, installing only necessary applications and updates.
- Deployment of New Systems: In a corporate environment, reimaging is commonplace for deploying multiple identical systems to ensure uniformity across the organization.
The Process of Reimaging
The reimaging process can be segmented into several distinct stages, each crucial in ensuring a successful outcome:
- Back-Up Data: Prior to embarking on the reimaging journey, it is imperative to back up all critical files and data. While the process typically involves overwriting existing data, precautions should be taken to secure important information.
- Creating a System Image: In organizations, IT departments often create a master system image that encapsulates the desired software and settings. This image serves as the ultimate template for reimaging.
- Booting from Recovery Media: To initiate the reimaging process, the computer is usually booted from recovery media, which could be a CD, USB, or network-based source that contains the system image.
- Reinstalling: Following the boot-up, the restoration process involves loading the system image onto the hard drive, effectively erasing any previous data and configurations.
- Restoring Files: After the reimaging is complete, previously backed-up data can be restored onto the newly configured system.
Advantages of Reimaging
The benefits of reimaging a computer are manifold:
- Enhanced Performance: A fresh installation often results in a system that runs faster and more smoothly, free from the burdens of accumulated software and temporary files.
- Improved Security: Reimaging eliminates viruses and malware that could compromise security, thus allowing users to restore their systems to a secure, stable state.
- Standardization: In a business context, reimaging fosters standardization across devices, which streamlines IT management and simplifies troubleshooting.
- Cost Efficiency: Rather than purchasing new hardware, reimaging often allows organizations to extend the life of existing machines by rejuvenating their software environment.
Potential Drawbacks and Considerations
Despite its advantages, reimaging is not without drawbacks:
- Data Loss: If important files are not backed up prior to the reimaging process, they are irretrievably lost.
- Time-Consuming: The process can be time-intensive, especially in larger environments where multiple systems require reimaging.
- Software Licenses: Post-reimaging, users may encounter issues with software licensing, requiring reactivation or reinstallation of certain applications.
Conclusion
In summary, reimaging a computer is a practical and often necessary procedure to restore or enhance system functionality. It serves as an effective solution for addressing a spectrum of issues, from malware removal to performance optimization. Understanding the intricacies of the reimaging process, alongside its advantages and disadvantages, empowers users to make informed decisions. Whether undertaken by individuals or IT departments, reimaging can significantly contribute to a reliable computing experience when executed judiciously.






This comprehensive explanation of reimaging a computer highlights its critical role in IT maintenance and management. By restoring systems to a clean, standardized state, reimaging not only resolves persistent technical issues such as system crashes and malware infections but also enhances overall performance and security. The detailed breakdown of when to consider reimaging helps users identify the right circumstances for this process, emphasizing its practicality for both personal and organizational use. Additionally, outlining the step-by-step procedure reinforces the importance of preparation, especially backing up important data to prevent loss. While there are potential drawbacks like time consumption and licensing challenges, the benefits-such as cost savings and improved system reliability-often outweigh these concerns. Overall, reimaging is a valuable tool that, when carefully applied, ensures smoother, safer, and more consistent computing environments.
Joaquimma-Anna’s article adeptly unpacks the concept of reimaging by emphasizing not only its technical process but also its strategic value in maintaining healthy computer systems. The comprehensive overview-from explaining system images to detailing ideal scenarios for reimaging-provides readers with clear guidance on when and why this solution is effective. By highlighting both the significant advantages, such as enhanced performance and security, and the potential risks, including data loss and software licensing hurdles, the piece strikes an important balance that encourages informed decision-making. Particularly in organizational settings, the emphasis on standardization and cost efficiency underscores how reimaging can streamline IT operations and extend hardware usability. This thoughtful exploration equips users with a well-rounded understanding, reinforcing that while reimaging is powerful, its success hinges on careful planning and execution.
Joaquimma-Anna’s article provides a thorough and insightful exploration of reimaging, effectively bridging technical details with practical considerations. The clear explanation of system images and the rationale behind reimaging enables readers to appreciate its role beyond mere troubleshooting-highlighting it as a strategic tool for enhancing system integrity and uniformity. By emphasizing scenarios like malware infections and system malfunctions, the article illustrates when reimaging is most beneficial. Moreover, detailing the step-by-step process underscores the critical importance of preparation, especially backing up vital data to avoid irreversible loss. The balanced discussion of advantages such as improved performance and security, alongside real-world challenges like software licensing and time investment, equips users with a realistic understanding of what to expect. This comprehensive coverage makes the topic accessible and actionable, benefiting both individual users and IT professionals in maintaining robust and efficient computing environments.
Joaquimma-Anna’s article provides an excellent and well-rounded exploration of computer reimaging, illuminating both its technical foundations and practical applications. The clear explanation of what constitutes a system image and how it is used to restore a computer underscores the significance of reimaging beyond mere troubleshooting-it emerges as a strategic approach to maintain system integrity, security, and performance. Highlighting scenarios such as malware removal, system malfunctions, and organizational deployments contextualizes the process for a variety of users. The step-by-step overview emphasizes the vital prerequisite of backing up data, which is crucial to prevent irreversible loss. Additionally, the balanced discussion of advantages paired with potential setbacks like time demands and licensing obstacles offers readers a realistic perspective. This comprehensive treatment empowers both IT professionals and individual users to make informed, deliberate decisions about when and how to employ reimaging as a reliable tool to rejuvenate and standardize computing environments.
Joaquimma-Anna’s article delivers a clear and insightful analysis of computer reimaging, expertly bridging technical concepts with practical uses. By demystifying the notion of a system image, the article helps readers understand how reimaging effectively resets a machine to a clean, stable state, removing issues like malware or system errors. The scenarios outlined-ranging from troubleshooting to organizational deployment-offer a well-rounded perspective on when this approach is most advantageous. Particularly valuable is the detailed walk-through of the reimaging process, which underscores the crucial step of backing up data to prevent irreversible loss. The balanced discussion of benefits, such as enhanced performance and security, alongside challenges like time investment and software licensing, equips users with a realistic view. This thoughtful and comprehensive treatment empowers both individuals and IT professionals to leverage reimaging confidently as a strategic tool for maintaining reliable and efficient systems.
Building on the detailed insights provided, this article by Joaquimma-Anna thoroughly unpacks the multifaceted nature of reimaging-a critical tool in today’s IT landscape. By clearly demystifying the system image concept, the author enables readers to understand how reimaging restores devices to a pristine state, effectively addressing persistent issues like software corruption and malware. The balanced exploration of when to reimage, including scenarios of system malfunctions and security breaches, ensures users recognize its practical applications. Equally important is the comprehensive walkthrough of the process, underscoring data backup as a non-negotiable step to avoid loss. The article’s nuanced discussion of advantages, such as enhanced performance and cost-effectiveness, alongside drawbacks like time requirements and licensing hurdles, presents a realistic and actionable guide. This empowers both individuals and IT professionals to leverage reimaging judiciously as a strategic approach to prolong system life and maintain consistent, high-functioning environments.
Building on the comprehensive insights shared by Joaquimma-Anna, this article adeptly clarifies the critical role of reimaging in both personal and organizational IT management. It emphasizes how restoring a system to a preconfigured image not only resolves software malfunctions and malware infections but also renews system performance and security. The clear explanation of system images demystifies the technical underpinnings, making the concept accessible to a broad audience. Importantly, the detailed step-by-step breakdown highlights the indispensable necessity of backing up data to prevent loss, a crucial safeguard often overlooked. Additionally, the article’s balanced discussion of benefits-like enhanced speed, security, and cost savings-against challenges, such as time consumption and license management, provides a realistic framework for users. Overall, this thoughtful and practical examination empowers readers to strategically leverage reimaging as a powerful tool for sustaining dependable and streamlined computing environments.
Adding to the insightful reflections already shared, Joaquimma-Anna’s article serves as a comprehensive guide that highlights the strategic importance of reimaging in modern computing. It effectively clarifies how reimaging not only remedies issues like malware infections and system malfunctions but also plays a vital role in standardizing setups across organizations, simplifying IT management. The stepwise explanation of the reimaging process is particularly valuable, as it stresses the often-underemphasized necessity of data backup-a step critical to safeguarding user information. Moreover, the balanced discussion of reimaging’s advantages, such as improved performance and cost efficiency, alongside potential hurdles like time consumption and licensing challenges, provides a practical framework that enables readers to weigh the decision carefully. Overall, this article equips users-from individuals to IT professionals-with the knowledge needed to employ reimaging effectively as a powerful tool for maintaining secure, reliable, and streamlined computing environments.
Adding to the thoughtful analyses already presented, Joaquimma-Anna’s article stands out for its clear, comprehensive breakdown of reimaging as both a technical procedure and strategic solution. It effectively captures the dual nature of reimaging: not only as a powerful remedy for issues like malware infections and system errors but also as a proactive approach to maintaining consistent performance, security, and standardization-especially in organizational contexts. The article’s structured presentation of the process, from essential data backup to restoring the system image, emphasizes best practices that mitigate risks such as data loss. Moreover, the balanced exploration of both benefits-like improved speed and cost-efficiency-and challenges-such as time consumption and software licensing-provides a nuanced perspective essential for informed decision-making. Overall, this exposition equips readers with practical insights that enhance their ability to leverage reimaging thoughtfully and effectively across diverse computing environments.
Building on the insightful reflections shared, Joaquimma-Anna’s article offers a thorough and accessible explanation of the reimaging process, emphasizing its transformative impact on computing environments. Highlighting both individual and organizational perspectives, the piece clarifies how reimaging serves as a critical solution-not just for resolving system errors, malware infections, or performance degradation-but also as a strategic approach for uniform IT deployment and ongoing system maintenance. The detailed breakdown of each stage-from backing up essential data to restoring the system image-reinforces best practices that safeguard user information while maximizing efficiencies. Furthermore, by balancing the clear advantages of enhanced speed, security, standardization, and cost savings against potential drawbacks such as data loss risks and time investment, the article equips readers with a pragmatic and informed framework. Overall, it empowers users and IT professionals alike to judiciously implement reimaging for sustainable, reliable computing performance.
Building on the comprehensive perspectives shared, Joaquimma-Anna’s article presents a well-rounded and accessible exploration of computer reimaging, highlighting its significance as both a restorative and preventive IT practice. By clearly defining the concept of a system image and explaining the step-by-step reimaging process, the piece equips readers with essential knowledge to safely and effectively implement this solution. The article thoughtfully addresses when reimaging is appropriate-ranging from combating malware to preparing corporate devices for deployment-while underscoring the critical importance of backing up data beforehand. Moreover, the balanced treatment of its advantages, such as improved performance, enhanced security, and cost savings, alongside practical challenges like time investment and software licensing concerns, ensures readers gain a realistic understanding. Overall, this insightful guide empowers individuals and organizations alike to make informed decisions about leveraging reimaging to maintain optimal, secure, and standardized computing environments.
Building upon the detailed and well-articulated overview provided by Joaquimma-Anna, this article offers an essential resource that demystifies the concept of reimaging for both individual users and organizations. The clear explanation of what constitutes a system image, paired with the methodical outline of the reimaging process, ensures readers understand the technical and practical steps involved. Highlighting key triggers for reimaging-ranging from system malfunctions and malware infection to organizational deployment needs-adds context to when and why this approach is most effective. Furthermore, by weighing the significant advantages, such as enhanced performance and improved security, against realistic considerations like potential data loss and time investment, the article provides a balanced perspective crucial for thoughtful decision-making. Overall, it empowers readers with the knowledge to approach reimaging not just as a repair tool but as a strategic solution for maintaining optimized, secure, and cost-efficient computing environments.
Building upon the comprehensive analysis by Joaquimma-Anna, this article thoroughly demystifies the concept of reimaging a computer, making it accessible and relevant for diverse users. It rightly emphasizes that reimaging is far more than a simple reset-it is a strategic process that addresses core issues like malware removal, system errors, and outdated configurations while enabling organizational uniformity and cost savings. The clear explanation of the system image concept and the step-by-step guidance on execution highlight essential best practices, particularly the critical importance of backing up data beforehand to avoid irreversible loss. The balanced evaluation of reimaging’s advantages-such as enhanced performance and improved security-against its potential downsides ensures readers are well-prepared to make informed choices. Overall, this insightful piece elevates understanding of reimaging as both a practical repair tool and a proactive method for sustaining optimized, secure computing environments.
Complementing the insightful reflections by previous commentators, Joaquimma-Anna’s article offers a clear and detailed exploration of computer reimaging, spotlighting its vital role in both troubleshooting and system management. The explanation of what constitutes a system image and the stepwise walkthrough demystify the process, making it approachable for users at varying levels of technical expertise. By outlining key scenarios for reimaging-from addressing malware to deploying standardized setups-this piece contextualizes when and why reimaging is strategically beneficial. Importantly, it balances the evident advantages, like performance enhancement and cost savings, with practical considerations such as the risk of data loss and the time required. This balanced perspective not only educates but empowers individuals and organizations to implement reimaging judiciously as a robust method to sustain optimized, secure, and standardized computing environments.
Expanding on Joaquimma-Anna’s comprehensive guide, it’s clear that reimaging plays a pivotal role in maintaining and optimizing computer systems in today’s tech-driven world. Beyond simply restoring systems, reimaging acts as a strategic reset that addresses both immediate issues like malware and long-term challenges such as system bloat and inconsistency across enterprise environments. The detailed process outlined-from data backup to final restoration-reinforces the importance of preparation and precision to avoid data loss and license complications. Additionally, the discussion of advantages highlights not only performance and security gains but also cost effectiveness, making reimaging a sustainable approach for prolonging hardware life. However, the candid acknowledgment of its time demands and risks ensures users approach it informed and cautious. Ultimately, this balanced perspective empowers individuals and IT teams to harness reimaging judiciously as a powerful tool for stable, secure, and standardized computing experiences.
Joaquimma-Anna’s comprehensive article provides a well-structured and insightful overview of the reimaging process, making it highly accessible for both individual users and IT professionals. By thoroughly defining what a system image entails and illustrating the step-by-step procedure, the piece demystifies a practice that is often seen as complex or daunting. The discussion of key scenarios-ranging from troubleshooting system issues and malware removal to large-scale corporate deployment-effectively contextualizes when reimaging is most advantageous. Importantly, the balanced analysis of benefits such as enhanced performance, improved security, and cost efficiency alongside practical considerations like data backup and time requirements offers readers a realistic and pragmatic understanding. This article stands out by empowering users with the knowledge to approach reimaging not merely as a reactive fix, but as a strategic tool for maintaining standardized, secure, and optimized computing environments.
Joaquimma-Anna’s article offers a thorough and well-structured examination of computer reimaging, presenting it as both a practical remedy for system issues and a strategic approach for maintaining optimal computing environments. The clear explanation of system images provides foundational understanding, while the detailed breakdown of the reimaging process makes this technical task approachable for a broad audience. By highlighting key scenarios such as malware removal, system malfunctions, and large-scale deployments, the piece effectively contextualizes when reimaging is most appropriate. Moreover, the balanced discussion of its benefits-ranging from improved performance and enhanced security to cost efficiency-along with potential drawbacks like data loss and time requirements, equips readers with a pragmatic perspective. This article serves as a valuable resource, empowering individuals and organizations to judiciously apply reimaging as an essential tool for sustaining reliable, secure, and standardized systems.
Adding to the insightful discourse already presented, Joaquimma-Anna’s article excels in clarifying the multifaceted nature of reimaging-a procedure that is pivotal for both individual users and organizations striving for reliable computer performance. The piece thoughtfully emphasizes that reimaging transcends a simple restoration; it is a strategic approach to eliminate persistent technical issues and standardize computing environments. I appreciate how the author underscores the critical need for data backup, a step often underestimated, ensuring users safeguard valuable information before undertaking reimaging. By thoroughly detailing the advantages such as security enhancement and cost efficiency, alongside acknowledging practical challenges like licensing and time consumption, the article fosters a realistic and proactive mindset. Ultimately, this well-rounded exploration equips readers with a solid foundation to confidently leverage reimaging as both a remedial and preventative measure in technology management.
Joaquimma-Anna’s article provides an excellent, comprehensive overview of computer reimaging, articulating its dual role as both a powerful troubleshooting method and a strategic approach to IT management. The clear explanation of what constitutes a system image and the methodical breakdown of the reimaging steps make this topic approachable, even for less technical readers. Moreover, the article astutely highlights the importance of data backup, reminding users that the process, while restorative, carries risks if precautions are not taken. By presenting real-world scenarios for when reimaging is effective, such as removing malware or standardizing systems in a corporate setting, the piece contextualizes its practical utility. The balanced discussion of benefits-including performance enhancement and cost savings-alongside potential drawbacks like software licensing challenges and time consumption, encourages a well-informed, deliberate decision-making process. Overall, this article equips readers with the knowledge to confidently and judiciously employ reimaging as a vital tool for maintaining stable, secure, and efficient computing environments.
Building on the detailed insights provided by Joaquimma-Anna, this article thoroughly demystifies the concept of reimaging-a vital practice that transcends simple system restoration to serve as a strategic method for troubleshooting, security enhancement, and uniform system deployment. The clear explanation of system images and the step-by-step breakdown of the reimaging process equip readers with practical knowledge applicable from personal computing to enterprise IT management. By carefully weighing benefits like improved performance, enhanced security, and cost efficiency against considerations such as backup necessity and time investment, it fosters a balanced understanding crucial for making informed decisions. This comprehensive overview highlights how reimaging, when executed with preparedness and precision, can significantly prolong hardware usability and maintain a reliable, standardized computing environment, empowering users and IT professionals alike to confidently incorporate it into their maintenance toolkit.
Building on the insightful analysis presented by Joaquimma-Anna, this exploration of reimaging unpacks a crucial IT practice that extends far beyond mere system restoration. Emphasizing the concept of a system image as a comprehensive snapshot, the article clarifies how reimaging resets computers to a known good state, effectively resolving persistent issues and reinforcing security. The detailed outline of when to consider reimaging-ranging from malware removal to large-scale deployment-provides practical guidance tailored to diverse contexts. Equally important is the step-by-step process, which underscores the necessity of data backup and preparation, helping users avoid common pitfalls such as data loss or licensing problems. Highlighting benefits like enhanced performance and cost savings alongside honest discussion of drawbacks offers a balanced and realistic perspective. Overall, this piece empowers readers with the knowledge and confidence to leverage reimaging as a strategic, proactive solution for maintaining efficient, standardized, and secure computing environments.
Expanding on Joaquimma-Anna’s comprehensive exploration of computer reimaging, this detailed overview highlights the critical role reimaging plays in both personal and organizational IT maintenance. By defining a system image as a complete snapshot of the operating environment, the article clarifies how reimaging effectively restores systems to a clean, stable state, resolving glitches and removing malware. The thoughtful guidance on when reimaging is advisable-such as during system malfunctions or for uniform system deployment-provides practical decision criteria. Importantly, the step-by-step process underscores the necessity of careful data backup and preparation to mitigate risks like data loss. Furthermore, by balancing clear benefits-including improved performance, enhanced security, and cost savings-with realistic drawbacks such as time investment and software licensing challenges, it equips readers with a nuanced understanding. This empowers users and IT professionals alike to harness reimaging not just as a cure for problems but as a strategic practice to maintain reliable, secure, and standardized computing environments.
Complementing the insightful analyses shared, this article by Joaquimma-Anna provides a thorough and accessible account of computer reimaging’s role in modern IT practices. By demystifying the concept of a system image as a full snapshot of the operating environment, it captures how reimaging can effectively resolve software malfunctions, eradicate malware, and restore systems to an optimal state. The methodical explanation of when and how to reimage equips readers with practical knowledge essential for thoughtful decision-making. In particular, emphasizing data backup as a crucial preparatory step safeguards against potential data loss, one of the process’s main risks. Moreover, balancing the clear benefits of enhanced performance, security, standardization, and cost savings against real-world challenges like time requirements and licensing intricacies encourages a nuanced understanding. This comprehensive perspective empowers both individual users and IT professionals to harness reimaging not just as a corrective action but as a strategic approach to maintaining secure, reliable, and efficient computing environments.
Adding to the comprehensive insights shared by previous commenters, this article by Joaquimma-Anna elegantly captures the multifaceted nature of computer reimaging, underscoring its vital role across both individual users and enterprise IT landscapes. The clear explanation of a system image as a complete snapshot helps demystify technical complexities, making the concept accessible to a broad audience. Highlighting practical triggers like system malfunctions, malware infections, and corporate deployment needs reinforces the real-world relevance of reimaging. Particularly valuable is the detailed walkthrough of the process-emphasizing data backup as a critical safeguard-which balances thoroughness with clarity. Furthermore, the balanced discussion around tangible benefits such as enhanced performance, improved security, and cost-effectiveness versus challenges like data loss risk and software licensing nuances fosters a measured understanding. Overall, this article empowers readers to approach reimaging not merely as a repair tool but as a strategic choice for sustaining reliable, secure, and standardized computing environments.
Adding to the insightful analysis by Joaquimma-Anna, this article offers a clear, well-structured overview of computer reimaging as both a practical remediation tool and a strategic IT approach. By thoroughly defining a system image and detailing the stepwise reimaging process, readers gain a solid grasp of how this operation effectively restores system health, eliminates malware, and standardizes configurations. The emphasis on data backup before reimaging underscores an often overlooked but critical precaution to prevent data loss. Equally important is the balanced presentation of benefits-such as enhanced performance, security, and cost-efficiency-alongside real challenges like time consumption and licensing complexities. This holistic perspective equips individual users and IT professionals with the confidence to view reimaging beyond mere troubleshooting, appreciating its role in sustaining optimized, secure, and consistent computing environments across various contexts.
Building upon the comprehensive insights of Joaquimma-Anna’s article, this well-structured explanation elucidates the critical role of reimaging in modern computing. By clearly defining a system image as a full snapshot of the operating environment, the article demystifies a complex concept, making it accessible for diverse audiences. The piece thoughtfully outlines when reimaging is advisable-such as in cases of software failures, malware infections, or corporate deployments-providing practical, real-world criteria. Importantly, the detailed breakdown of each stage in the reimaging process, particularly the emphasis on data backup, equips readers with essential precautions to minimize risk. Moreover, the balanced presentation of benefits like performance boosts, improved security, cost efficiency, alongside potential downsides such as data loss and licensing challenges, encourages informed, strategic decision-making. This article ultimately frames reimaging as both a powerful remedial tool and a proactive IT practice that supports reliable, secure, and standardized computing environments.
Building on the detailed analysis by Joaquimma-Anna, this article offers a clear and insightful breakdown of the concept and practice of computer reimaging. It goes beyond merely defining reimaging-explaining how a system image encapsulates the entire operating environment-to contextualize when and why this process becomes essential. Particularly useful is the structured overview of scenarios that warrant reimaging, from troubleshooting persistent system faults to ensuring security through malware elimination. The meticulous stepwise explanation, highlighting critical preparatory actions like data backup, equips readers with a practical understanding that reduces risks associated with the process. By weighing the tangible benefits-such as enhanced system performance, security, and cost efficiency-against potential drawbacks like data loss and licensing issues, the article fosters a balanced perspective. Overall, it effectively positions reimaging not just as a remedial intervention but as a strategic tool supporting dependable, streamlined, and secure computing environments.
Building on the thorough exploration by Joaquimma-Anna, this article offers an essential and comprehensive guide to the concept and practicalities of computer reimaging. By clearly defining what a system image entails, it lays a solid foundation for readers to understand why and when reimaging becomes crucial-from resolving persistent system issues to combating malware and preparing devices for uniform deployment in business settings. The careful delineation of the reimaging process, especially emphasizing the indispensability of backing up data, provides valuable preventive insights that mitigate risks like data loss. Additionally, the balanced discussion of benefits-including improved performance, enhanced security, and cost savings-alongside considerations such as time consumption and licensing challenges, promotes an informed and strategic approach. Overall, this article equips both individual and corporate users with the knowledge to utilize reimaging effectively as a key tool for maintaining optimized, secure, and standardized computing systems.
Building on Joaquimma-Anna’s comprehensive overview, this article provides an excellent blend of technical clarity and practical guidance on computer reimaging. By thoroughly defining the system image and detailing when and why reimaging should be considered, it demystifies a process often seen as complex. The step-by-step breakdown-from critical data backup to restoration-ensures readers appreciate the importance of each stage in safeguarding data and achieving a smooth recovery. Moreover, the balanced discussion of advantages like improved system speed, enhanced security, and organizational standardization alongside potential challenges such as data loss and licensing issues offers a realistic perspective. This thoughtful approach not only informs users about the technical process but also encourages strategic decision-making. Ultimately, the article strengthens understanding of reimaging as both a powerful troubleshooting method and a proactive IT practice that benefits individuals and enterprises alike.
Adding to the comprehensive insights provided by Joaquimma-Anna, this article offers a well-rounded and accessible explanation of reimaging that resonates with both individual users and IT professionals. By clearly defining the concept of a system image and illustrating practical scenarios where reimaging proves essential, it effectively clarifies a process often viewed as complex or daunting. The detailed step-by-step guide, especially emphasizing the importance of data backup, is invaluable in reducing risk and ensuring a successful restoration. Additionally, the balanced discussion of the numerous advantages-like improved system performance, security enhancements, and organizational standardization-alongside potential downsides such as data loss and licensing challenges, forms a realistic and strategic outlook. This thoughtful exposition not only educates readers on technical whys and hows but also encourages proactive decision-making to optimize computing reliability and longevity.
Adding to the insightful analyses by previous commentators, Joaquimma-Anna’s article serves as a thorough and practical guide to the intricate process of computer reimaging. It excels in breaking down a technically complex topic into clear, accessible segments that resonate with both everyday users and IT professionals. The emphasis on understanding what constitutes a system image provides a solid conceptual foundation, while the outlined scenarios for when to consider reimaging help readers apply this knowledge contextually. The detailed five-step process thoughtfully prioritizes data backup, addressing a common pitfall that can lead to severe data loss. Furthermore, the balanced discussion of benefits-ranging from enhanced performance and security to organizational standardization-and the candid acknowledgment of challenges like licensing and time requirements, equips readers for realistic expectations. Altogether, this article encourages informed, strategic decisions, positioning reimaging not just as a remedial tactic but as a key element in maintaining optimal, secure, and efficient computing environments.
Adding to the thoughtful perspectives shared by previous commentators, Joaquimma-Anna’s article delivers an exceptionally well-structured and comprehensive examination of computer reimaging. It excels at demystifying a technically intricate procedure by grounding it in clear definitions and relatable scenarios, making the topic accessible for both novices and IT experts. The emphasis on careful preparation-especially backing up data-is crucial and highlights a common, often overlooked, vulnerability in the reimaging process. The article’s balanced approach to outlining both the significant advantages (performance improvement, security enhancement, cost-effectiveness, and standardization) and the realistic challenges (potential data loss, time investment, and licensing hurdles) encourages readers to make well-informed, strategic decisions. Ultimately, this piece not only educates but also empowers users and organizations to employ reimaging proactively as a vital component of maintaining resilient, efficient, and secure computing environments.
Adding to the insightful reflections already shared, Joaquimma-Anna’s article stands out for its meticulous yet accessible breakdown of the reimaging process. The clear definition of a system image sets a strong contextual foundation, enabling users to grasp the technical nuances without feeling overwhelmed. The thoughtful identification of scenarios warranting reimaging helps readers connect theory with practical decision-making. Emphasizing data backup as the initial critical step reinforces a preventative mindset essential to protecting valuable information. Moreover, the article’s balanced portrayal of benefits-such as enhanced performance, security, and standardization-alongside candid acknowledgment of potential drawbacks like data loss and licensing hurdles, encourages a well-rounded understanding. By combining technical detail with pragmatic guidance, this piece equips individuals and organizations alike to strategically employ reimaging, thereby fostering more reliable, secure, and efficiently managed computing environments.
Adding to the detailed and insightful reflections already provided, Joaquimma-Anna’s article stands out for its clarity and thoroughness in explaining the complex concept of computer reimaging. The article’s strength lies in breaking down technical jargon-like the notion of a “system image”-into understandable segments that resonate with both casual users and IT professionals. By outlining practical scenarios for when reimaging is advisable, such as malware infection or system malfunctions, it grounds theoretical knowledge in real-world application. The step-by-step process, especially the emphasis on backing up data beforehand, addresses critical risks effectively. Furthermore, the balanced exploration of advantages-enhanced performance, security, and uniformity-alongside challenges like data loss and licensing issues, provides a well-rounded perspective. This thoughtful exposition equips readers to approach reimaging strategically, ensuring optimal system reliability and longevity whether at home or in organizational settings.
Building on the comprehensive and insightful explorations already shared, Joaquimma-Anna’s article masterfully dissects the multifaceted concept of computer reimaging with clarity and precision. The clear explanation of what constitutes a system image provides a foundational understanding that demystifies this often misunderstood process. The article’s practical framing-highlighting key scenarios for reimaging such as malware removal, performance optimization, and organizational deployment-bridges theory with real-world application seamlessly. The systematic breakdown of the process steps, particularly the essential emphasis on data backup, addresses critical user concerns about data safety. Furthermore, by weighing both the significant advantages like enhanced security and performance against potential drawbacks such as time investment and licensing issues, the piece equips users to make balanced and informed decisions. This thorough and accessible guide ultimately empowers readers to leverage reimaging effectively, promoting more secure, reliable, and streamlined computing experiences across diverse contexts.
Building on the comprehensive insights already shared, Joaquimma-Anna’s article brilliantly demystifies the concept of computer reimaging by blending technical depth with practical clarity. The clear explanation of a system image sets a solid foundation, allowing readers at all levels to understand how reimaging effectively resets a computer to a clean, optimized state. Highlighting scenarios such as malware removal and system malfunctions makes the topic immediately relevant, while the step-by-step walkthrough-especially the emphasis on data backup-addresses critical precautions often overlooked. Importantly, by balancing the notable advantages like improved security, performance, and cost savings against potential challenges such as data loss and licensing complexities, the article fosters a nuanced perspective. This thoughtful, well-structured exposition empowers individuals and organizations to use reimaging as a strategic tool for maintaining reliable, secure, and efficient computing environments.
Building on the comprehensive analyses so far, Joaquimma-Anna’s article provides an exceptionally clear and methodical exploration of the reimaging process, making a complex IT concept both approachable and practical. The thorough explanation of a system image as a foundational element helps readers understand how reimaging effectively resets a device to an ideal state, eliminating common software issues and security threats. The well-articulated scenarios for reimaging-ranging from malware removal to organizational deployment-offer valuable context for when and why this process is necessary. Importantly, the step-by-step breakdown reinforces best practices like data backup, which is critical to avoiding irreversible loss. By addressing both the tangible benefits such as enhanced performance and standardization, and the realistic challenges like time consumption and licensing, the article equips readers to make informed decisions about incorporating reimaging into their maintenance routines. This balanced and insightful guide stands out as an essential reference for individuals and IT professionals aiming to optimize system reliability and security.
Building upon the insightful analyses already shared, Joaquimma-Anna’s article offers a clear and comprehensive exploration of computer reimaging, effectively bridging the gap between technical complexity and practical application. The emphasis on understanding a system image as the cornerstone of reimaging deepens readers’ grasp of how this process serves as a reset button for computing environments. By thoughtfully identifying common scenarios like malware infections, system malfunctions, and large-scale deployments, the article grounds reimaging in real-world relevance. Its detailed, step-by-step outline-particularly the critical reminder to back up data-reinforces prudent preparation that is often overlooked. Balancing the advantages of improved performance, security, and cost efficiency against potential challenges, such as data loss and licensing issues, the article equips users with a realistic and strategic perspective. This well-crafted guide empowers both individuals and IT professionals to utilize reimaging judiciously, enhancing system reliability and security.
Building on the insightful perspectives shared thus far, Joaquimma-Anna’s article offers a thorough and accessible explanation of computer reimaging, making a complex IT procedure approachable for users at all levels. The clear definition of a system image as a foundational element effectively clarifies how reimaging restores a device to a clean, optimized state. By identifying practical scenarios for reimaging-ranging from resolving software malfunctions and malware infections to deploying uniform systems in organizations-the article demonstrates its real-world applicability. The detailed, stepwise guide, particularly the crucial emphasis on data backup, underscores responsible preparation to prevent data loss. Additionally, weighing the considerable benefits such as improved security, enhanced performance, and cost efficiency against challenges like licensing and time investment equips users with a balanced understanding. This well-rounded approach empowers both individuals and IT professionals to leverage reimaging strategically for maintaining secure, reliable, and efficient computing environments.
Adding to the thoughtful reflections above, Joaquimma-Anna’s article stands out for its thorough and accessible treatment of reimaging, covering both conceptual and practical facets with clarity. By demystifying the notion of a system image, the article lays a firm foundation, helping users understand the transformative nature of reimaging as a way to restore and optimize computers. The well-chosen examples – from resolving malware infections to deploying standardized systems across organizations – ground the discussion in everyday relevance. Additionally, the careful step-by-step explanation, with a strong emphasis on data backup, highlights essential preparation that safeguards against data loss. Addressing the balance between clear advantages like improved performance and security and the potential downsides such as time consumption and license management provides readers with a realistic, strategic perspective. This comprehensive treatment equips both individuals and IT professionals to confidently integrate reimaging into their maintenance and deployment workflows, ultimately fostering more secure, efficient, and reliable computing environments.
Adding to the detailed and insightful commentary already provided, Joaquimma-Anna’s article excels in making the concept of reimaging accessible yet comprehensive for both novices and IT professionals. The clear definition of a system image as the backbone of the reimaging process is particularly valuable, as it clarifies how a device can be reverted to a trusted baseline state. The selection of real-world scenarios-from troubleshooting persistent system errors and eradicating malware to standardizing devices across enterprises-demonstrates the practical relevance of reimaging in diverse contexts. Moreover, the methodical breakdown of the process, especially the emphasis on data backup, reflects a responsible approach that mitigates risk. Highlighting both the considerable advantages-such as improved performance, security, and cost effectiveness-and acknowledging potential challenges like time investment and software licensing, the article equips readers with a balanced, realistic framework. This makes it an essential reference for anyone seeking to understand or implement reimaging effectively.
Adding to the thoughtful reflections provided, Joaquimma-Anna’s article offers a lucid and comprehensive overview of reimaging that demystifies this vital IT process for users and professionals alike. The clear explanation of a system image as a holistic snapshot underpins the reader’s understanding, while the real-world scenarios help contextualize when and why reimaging is indispensable-from fixing persistent errors and removing malware to large-scale corporate deployments ensuring uniformity. The stepwise process with a strong emphasis on data backup underscores responsible planning, which is crucial given the risk of data loss. Furthermore, the balanced examination of advantages-like improved system performance, security, and cost savings-and potential challenges such as licensing issues and time investment equips readers with a practical framework for making informed decisions. Overall, this article serves as a valuable guide that enhances both knowledge and confidence in employing reimaging effectively.
Building upon the comprehensive insights provided by Joaquimma-Anna, this article excellently unpacks the multifaceted essence of reimaging, bridging both conceptual understanding and practical application. Defining a system image as a full snapshot underscores its critical role as a baseline for restoring systems, which is vital for both troubleshooting and standardized deployments. The clear categorization of scenarios-ranging from mitigating malware effects to refreshing outdated configurations-highlights the versatile relevance of reimaging in everyday and enterprise contexts. Emphasizing meticulous steps, especially the paramount importance of data backup, showcases responsible IT practices that mitigate risk. Moreover, the balanced discussion of benefits such as enhanced performance, security, and organizational uniformity alongside challenges like data loss and licensing complexities provides readers with a nuanced perspective. Overall, this piece serves as an essential resource that empowers individuals and IT professionals to approach reimaging thoughtfully and strategically, ensuring optimized and secure computing environments.
Building on the detailed analysis presented by Joaquimma-Anna, this article adeptly clarifies the vital concept of reimaging, making it accessible for both individual users and IT professionals. By defining a system image as a comprehensive snapshot of an entire computer setup, the piece underscores the reliability of this method for restoring systems to a known good state. The clear identification of scenarios-such as addressing malware infections, resolving persistent software glitches, and deploying standardized setups in corporate environments-illustrates its diverse applications. The structured breakdown of the reimaging process, with an emphasis on data backup, highlights the importance of thorough preparation to avoid data loss. Furthermore, the balanced discussion of advantages like enhanced security, performance, and cost savings alongside potential drawbacks like time consumption and licensing complexities offers a nuanced perspective. Overall, this article serves as an essential, practical guide for anyone seeking to understand and implement reimaging effectively and responsibly.
Building upon the comprehensive analysis by Joaquimma-Anna, this article offers a clear, well-structured exploration of reimaging that effectively bridges theory and practice. Highlighting the critical role of a system image as a full snapshot of an operating system, applications, and settings gives readers a solid understanding of how reimaging restores devices to a known good state. The detailed scenarios illustrate its wide applicability-from combating malware and troubleshooting persistent issues to rolling out standardized environments in enterprises. Emphasizing the stepwise process, especially the crucial data backup stage, reinforces responsible IT hygiene and risk mitigation. Moreover, the balanced discussion of benefits like improved system performance, enhanced security, and cost savings alongside potential challenges such as time consumption and licensing concerns enables informed decision-making. Overall, this article serves as an essential guide for both individuals and organizations seeking to implement reimaging efficiently and strategically.